Outcome
- Vulnerability report.
- Severity-based “prioritization” of remediation task.
- Regular consultation with Sterling Security Analysts.
Outcome
- A clear and concise strategic view of your organization’s cyber risk landscape.
- Executive cyber security dashboard.
- Vulnerability reports with detailed remediation guidance (in-line with major compliance requirements, i.e. FFIEC, OFSI, GLBA etc.)
- Risk-based prioritization of remediation tasks.
- Remediation Verification.
- Regular consultation with Sterling Security Analysts.
- Unlimited scanning of IT systems for vulnerabilities.
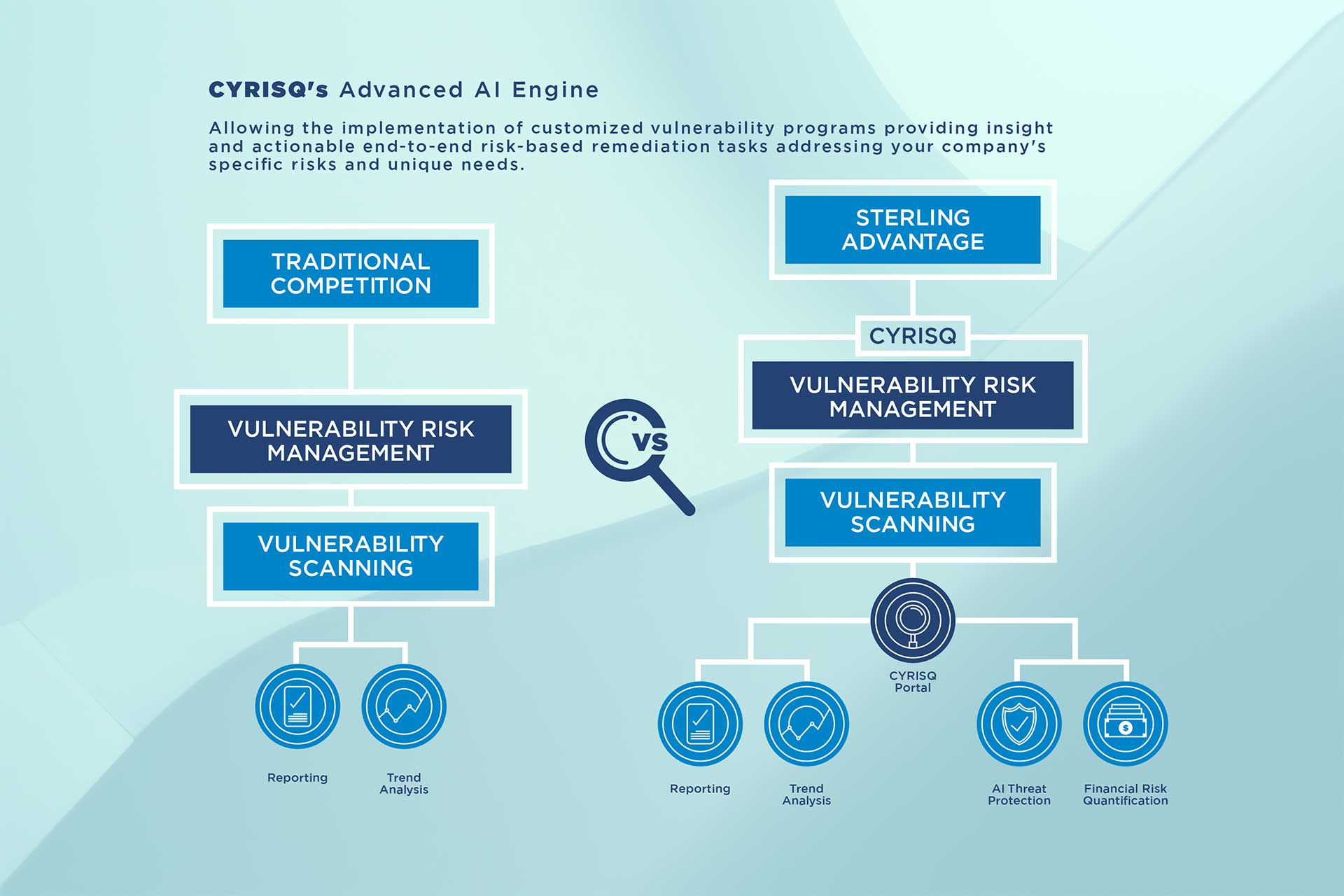
Organizations are now adopting the practice of regular vulnerability scanning to combat cyber threats however,
- Vulnerability management is complex.
- Vulnerability scanning is just a component.
Without the staff, budget and technology to support the changing infrastructure, organizations are still left exposed.
That's were we come in:
Our cyber security expertise has shaped our advanced AI engine allowing:
- Implementation of customize vulnerability management programs;
- provide insight and actionable end-to-end risk-based remediation tasks;
- Address your company’s specific risk and unique needs.
What we do:
- Discover your assets/hosts.
- Understand your business context and classify.
- Scan and discover vulnerabilities.
- Eliminate false positives
- Report risk and vulnerabilities.
- Provide continuous analysis and metrics.
What you get:
- Executive cyber security dashboard.
- Vulnerability reports with detailed remediation guidance (in-line with major compliance requirements, i.e. FFIEC, OFSI, GLBA etc.)
- Risk-based prioritization of remediation tasks.
- Remediation verification.
- Regular consultation with our Security Analysts.
- Unlimited scanning of IT systems for vulnerabilities.
How you benefit:
- Increase budget and resources to work on other important projects.
- Clear insight into your company’s security vulnerabilities and business risk.
- Straightforward action plan to mitigate your company’s security risk.
- Stay up-to-date on new vulnerabilities and ways to manage them.
- Achieve your company’s compliance mandates from regulatory bodies such as FFIEC, OFSI, GLBA etc.
- Access to over 50 years of combined risk expertise from our security analysts.


