Reading Time: 4 minutes
Countless network security breaches had occurred in the internet space over the years, leaving behind devastating consequences. According to a study, the odds of experiencing a data breach are 1 out of 4. The same study also revealed that, on average, businesses are spending $7.2 million on security breaches. That goes to show how hazardous network security threats can be for your business if left unchecked.
Since cybersecurity breach is an unforeseeable threat, as a business owner – whether you own a corporation or small to medium-sized business – you should build strong network security defenses around your company’s network.
The most effective way to combat network security threats is to know the various threat-proof techniques that are most applicable for your business and be proactive at implementing them. At the same time, you can always sign up for a network security engineer course, which will teach you everything you need to know about network security.
Popular Network Threats
How to Stop Network Security Threats
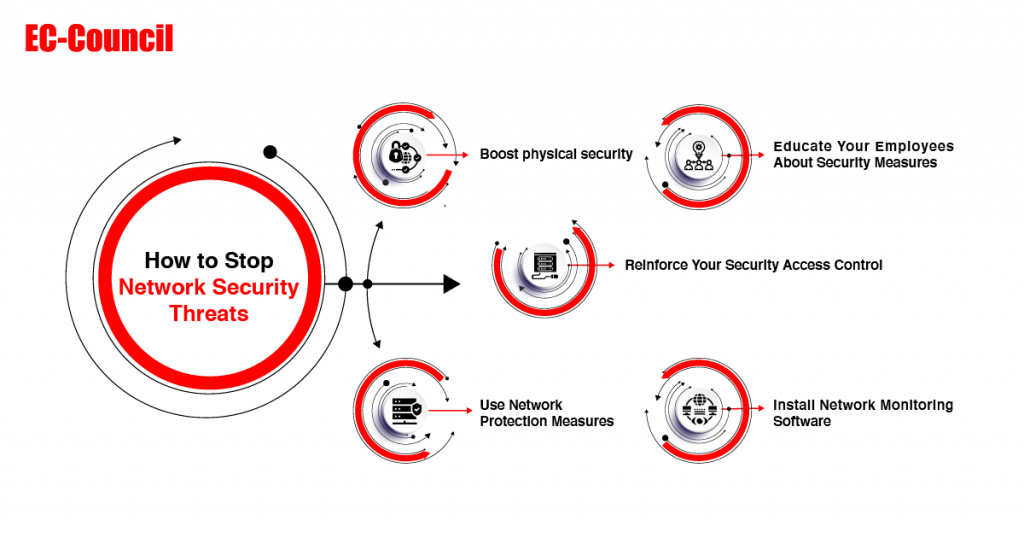
1. Boost physical security
If you install your network server(s) within the premise of your company, ensure you secure the facility tightly. You may need to hire security guards to protect and prevent insider incidents. You may also install a reliable digital lock, strong enough to discourage network intruders from having physical access to your servers.
2. Educate Your Employees About Security Measures
Taking up an advanced network security course such as Certified Network Defender will upskill your network administrator with adequate network security skills to defend your organization against vicious attacks. This is the perfect way to ensure they’re up to date with the newest technologies. Apart from your network administrator, you should provide training to all your employees. Incentivize them on network various types of network security attacks, how to identify threats, and whom to contact. Follow up on the training, updating your employees about the latest potential security threats.
3. Reinforce Your Security Access Control
Often, network security breaches occur when an unauthorized person gained access to the company’s passwords. In that case, ensure you create a unique password for each system, using a combination of lower case letters, upper case letters, special characters, and numeric characters. Ensure that all default passwords are changed to secure passwords. In many instances, change your passwords frequently, and always keep them away from authorized eyes. You can also adopt multilevel authentication alongside the fingerprint scanner. This can serve as an additional layer of security to further bolster the overall network security of your company.
4. Use Network Protection Measures
Network security protection measures are part of your first line of defense against cyber attackers. Take note of the following actions that’ll help enhance your network security:
- Conduct proper maintenance, such as updating outdated software
- Install a firewall
- Use IDS/IPS to help tract potential packet floods
- Use network segmentation
- Install a Virtual Private Network (VPN)
5. Install Network Monitoring Software
Network monitoring software provides early warning at the slightest instance of detecting a threat. It does this by keeping track of the entire IT infrastructure, establishing contact with all devices, and the system.
The network monitoring software covers three critical areas of your network:
- Monitors the entire security systems: It regularly scans your system firewalls and virus scanners to ensure operational reliability.
- Measures bandwidth bottlenecks: Malware attack could slow down system response time, allowing the attacker to steal or control sensitive data. The monitoring software checks for inconsistency on your system and report them, allowing the administrator to analyze the data and quickly act on it.
- Inspects environmental parameters: Network monitoring software enables surveillance to check all surrounding areas. Some monitoring software is built with sensory technology to detect smoke or gas formation.
Some of these specialized devices can be configured to trigger an alarm once it detects security breaches such as when the door or window of your server is opened.
Become a Certified Network Defender
EC–Council’s Certified Network Defender course is a 14- module packed program that’ll provide you – whether you’re a network administrator, CND analyst, or involved in any network operations – with the hands-on Network Security Training to attain Defense-in-Depth network security preparedness. You can also choose from the array of training options that suits your circumstances.
What are network security threats?What is the biggest threat to network securi